LEGO Classic - Caja de Ladrillos Creativos Mediana - 10696 | Lego Bloques Y Bases | Toys"R"Us España

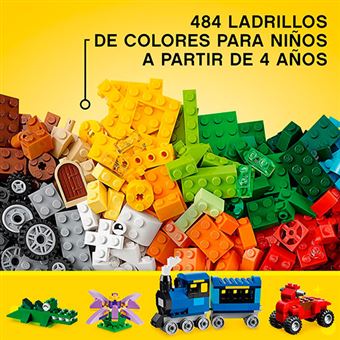
Buy LEGO® Creative Bricks Box Medium - Caja de Ladrillos Creativos Mediana online for26,99€ | AK-Interactive

Buy LEGO® Creativity Toolbox Maker - Creación: Caja de herramientas creativa online for53,99€ | AK-Interactive

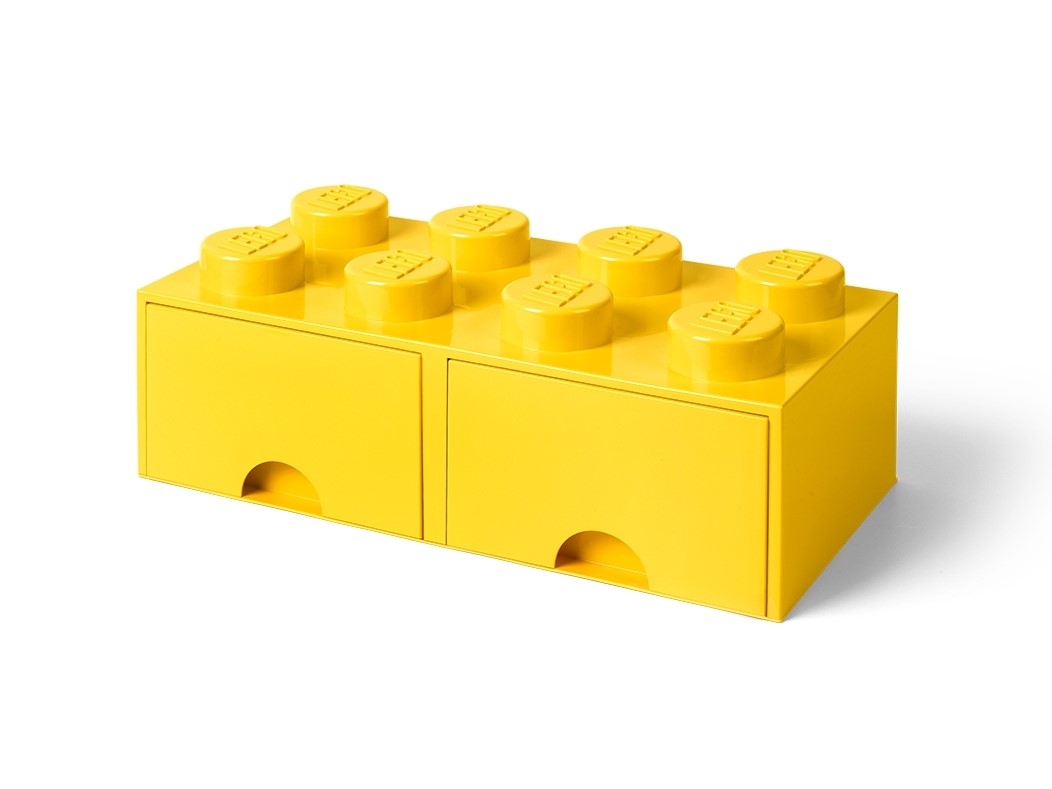
Lego - Caja De Almacenaje Con Diseño De Ladrillo 2 Negro 40021733 con Ofertas en Carrefour | Ofertas Carrefour Online

Buy LEGO® Creative Bricks Box Large - Caja de Ladrillos Creativos Grande online for44,99€ | AK-Interactive